This article, written by the leading blockchain security company SlowMist Technology, provides a detailed introduction to various types of wallets, including browser wallets, mobile wallets, hardware wallets, and web wallets that are not recommended for use. The article also discusses common risks faced by wallets, such as accidentally downloading fake wallets, computers being affected by malware, and potential security vulnerabilities in wallets themselves.
(Background:
What can we expect from the next Ethereum upgrade, “Pectra”? Staking mechanism, wallet user experience..)
Table of Contents
Wallet Categories
Browser Wallets
Web Wallets (Not Recommended)
Mobile Wallets
Desktop Wallets
Hardware Wallets
Paper Wallets (Not Recommended)
Common Wallet Risks
Downloading Fake Wallets
Purchasing Fake Wallets
Computer Malware
Wallet Vulnerabilities
Conclusion
With the cryptocurrency market becoming increasingly popular, Web3 projects and gameplay are evolving rapidly, and players’ emotions are running high. Along with this, players may accidentally fall into traps or become victims of phishing attacks while participating in various new projects. In this context, combined with the information we have collected both online and offline, we hope to expand a series of educational examples related to user asset security. Thus, the Web3 Security Beginner’s Guide was created.
We plan to comprehensively integrate various risk points in the Web3 field and use examples to help readers better identify and prevent risks. The main content of this guide includes, but is not limited to, risks during wallet downloads and usage, pitfalls that may be encountered when participating in various Web3 ecosystem projects, how to better identify dangerous signature authorizations, and remedies in the unfortunate event of theft. (Note: The content is subject to change based on the pace of development and the author’s ideas, so the final content may be more or less than planned).
Whether you are a novice who wants to explore the unknown and exciting Web3 world but are confused by industry jargon, different gameplay from Web2, and unknown risks, or a Web3 veteran who has been venturing in the dark forest of blockchain for a while, having heard and experienced many “traps” but still unclear about the reasons for being hacked and how to prevent further damage, you can learn from this guide. The aim of this guide is to help every user better protect their assets and navigate further in the blockchain dark forest.
As we all know, wallets are the gateway to the crypto world and the foundation of Web3 infrastructure, so their importance is self-evident. Without further ado, let’s introduce the first “appetizer” – wallet classification and risks.
Browser wallets, such as MetaMask and Rabby, are browser extensions installed in users’ browsers (such as Google Chrome and Firefox). Browser wallets are usually easier to access and use, and do not require additional software downloads or installations.

(https://metamask.io/download/)
Web wallets allow users to access and manage their crypto assets through web browsers. Although this method is more convenient, the associated risks should not be overlooked. Web wallets generally encrypt mnemonic phrases and store them locally in the browser, making them susceptible to threats from malicious software or network attacks.

(https://www.myetherwallet.com/wallet/access/software?type=overview)
Mobile wallets operate in a similar way to web wallets and are usually provided as mobile applications that users can download and install on their phones.

(https://token.im/download?locale=en-us)
Desktop wallets were more common in the early days of cryptocurrencies and include well-known wallets such as Electrum and Sparrow. These wallets are installed as applications on computers, and private keys and transaction data are stored locally on users’ devices, giving users complete control over their crypto private keys.

(https://sparrowwallet.com/)
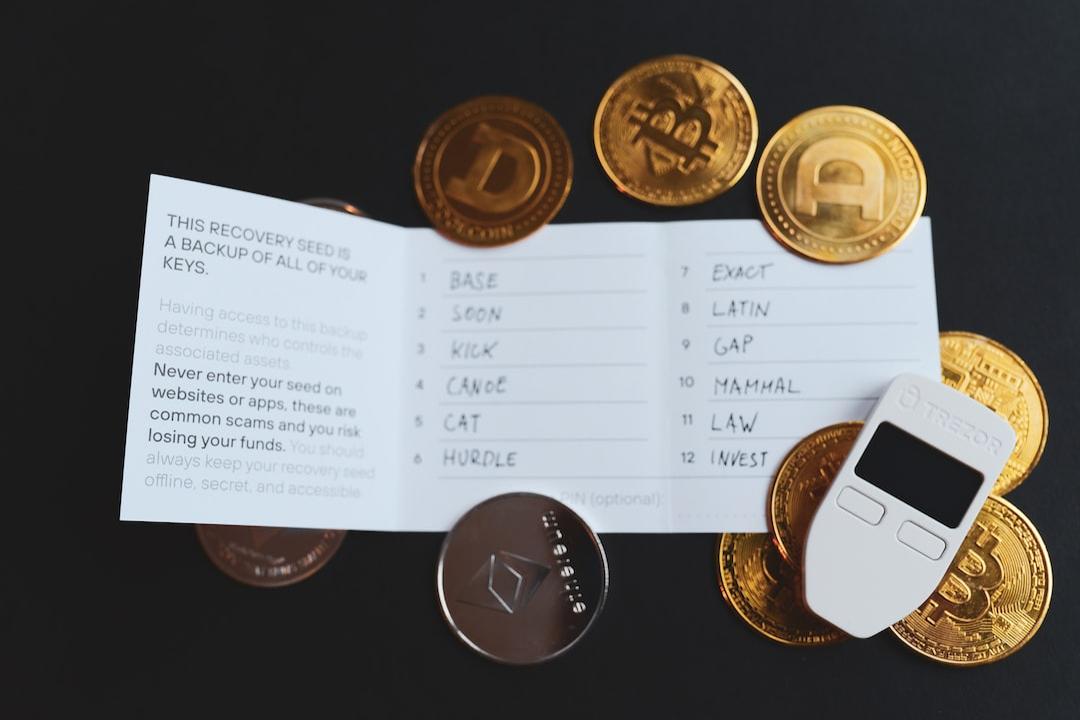
Hardware wallets are physical devices used to store cryptocurrencies and digital assets, such as Trezor, imKey, Ledger, Keystone, and OneKey. Hardware wallets provide an offline storage method for private keys, meaning that private keys are not exposed online when interacting with DApps using hardware wallets.

(https://shop.ledger.com/products/ledger-nano-s-plus/matte-black)
Paper wallets involve printing the cryptocurrency address and its private key as a QR code on a piece of paper, which can be used to conduct cryptocurrency transactions by scanning the QR code.
(https://www.walletgenerator.net/?culture=zh¤cy=bitcoin)
Many people download wallets from other sources, such as third-party download sites or by searching for a specific wallet in a browser and randomly clicking on a highly ranked link. This often leads to downloading a fake wallet because advertising space and organic traffic on search engines can be purchased. Scammers can buy top-ranked ad placements and create fake wallet websites to deceive users. The following image shows the search results for the TP wallet on Baidu:

(https://mp.weixin.qq.com/s/NdwIE412MJ7y-O5f2OrSHA)
Supply chain attacks are one of the main threats to the security of hardware wallets. If users do not purchase hardware wallets from official stores or authorized distributors, there is uncertainty regarding how many people have handled the wallet before it reaches the user’s hands and whether internal components have been tampered with. In the image below, the hardware wallet on the right has been tampered with.

(https://www.kaspersky.com/blog/fake-trezor-hardware-crypto-wallet/48155/)
If a computer is infected with malware, the wallet can be affected by malicious software. The SlowMist Security team has previously written a detailed analysis of the formation process and impact of the Redline Stealer malware in the article “Night Thief: Redline Stealer Malware Analysis”. Interested readers can view the article. We recommend users to install antivirus software such as Kaspersky, AVG, and 360, keep real-time protection enabled, and regularly update virus databases.
Lastly, even if you download a legitimate wallet, use it carefully, and have a secure device and environment, if there are design flaws in the wallet itself, it can still be targeted by hackers and users of that wallet can suffer asset losses. That’s why when choosing a wallet, convenience should not be the only consideration, and the open-source nature of the wallet’s code should also be taken into account. External developers and auditors can discover potential vulnerabilities through open-source code, reducing the likelihood of wallet attacks. Even in the unfortunate event of a wallet being hacked due to vulnerabilities, security personnel can quickly locate the vulnerabilities and provide timely remedies.
In this article, we mainly introduced wallet classification and listed common risk points to help readers form a basic understanding of wallet security. Regardless of the type or brand of wallet chosen, mnemonic phrases and private keys should always be kept confidential and secure. It is recommended to consider integrating the advantages of different types of wallets and using multiple types of wallets in combination. For example, using a well-known hardware wallet + well-known software wallet combination to manage significant assets, and using multiple well-known software wallets for managing smaller assets. In the next issue, we will provide a detailed introduction to the pitfalls of downloading and purchasing wallets. Stay tuned. (Note: The wallet brands and images mentioned in this article are for illustrative purposes only and do not constitute endorsements or guarantees.)
Related Articles
What’s next for Ethereum: EIP-3074 included in the Prague upgrade, bringing three major reforms to smart contracts and wallets.
TON ecosystem overview: 19 tracks covering Staking, DEX, wallets, launchpads, NFTs.
Is the FTX liquidation wallet a “downward indicator”? Precisely depositing 2500 ETH into the exchange before a crash.